[Editor – The NGINX ModSecurity WAF module for NGINX Plus officially went End-of-Sale as of April 1, 2022 and is transitioning to End-of-Life effective March 31, 2024. For more details, see F5 NGINX ModSecurity WAF Is Transitioning to End-of-Life on our blog.]
We are pleased to announce that NGINX ModSecurity Web Application Firewall (WAF) is now part of the Google Cloud Security Partner Ecosystem. NGINX ModSecurity WAF has been validated by both NGINX, Inc. and Google as a solution for protecting Google Cloud Platform (GCP) applications from Layer 7 attacks, such as SQL injection (SQLi) and remote code execution (RCE).
“We’re proud to be partnering with Google to bring the advanced capabilities of NGINX Plus to the Google Cloud Platform,” said Paul Oh, head of Business Development at NGINX. “NGINX was one of the inaugural members in the Google Cloud Marketplace and we look forward to continuing to collaborate on improving our capabilities for mutual customers.”
What Is NGINX ModSecurity WAF?
NGINX ModSecurity WAF is our build of the well‑known and respected ModSecurity software and loads directly into NGINX Plus as a dynamic module. Originally a plug‑in for the Apache HTTP Server, ModSecurity was rewritten in version 3.0 to work natively with NGINX Plus and NGINX Open Source.
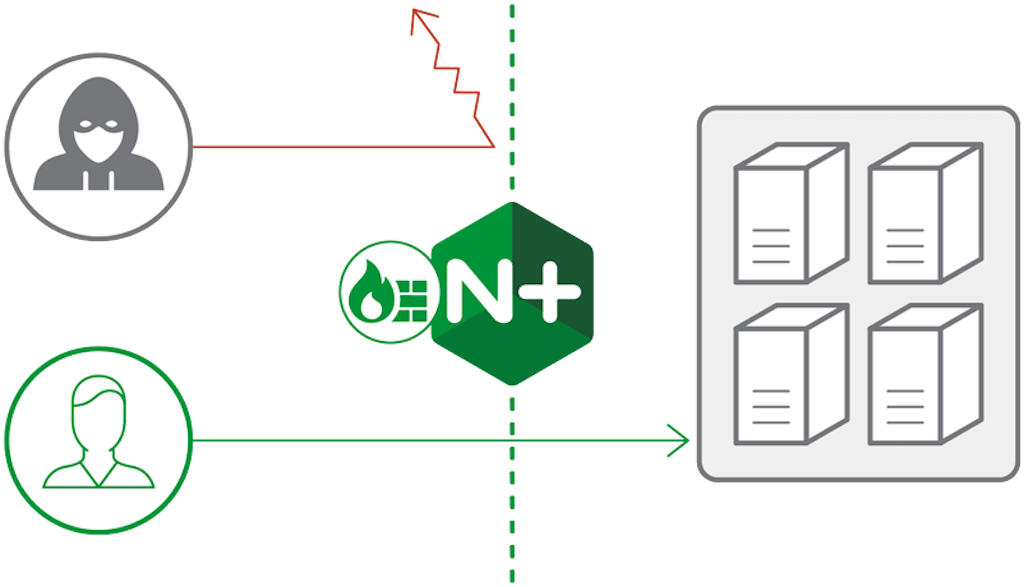
A WAF is a widely used solution for improving web application security. NGINX ModSecurity WAF is specialized to focus on HTTP traffic. When an HTTP request is made, NGINX ModSecurity WAF inspects all parts of the request for any malicious content or anomalies in the traffic. If the packet is deemed malicious it can be blocked, logged, or both, depending on configuration.
NGINX ModSecurity WAF uses a database of “rules” that define malicious behaviors. It supports the OWASP ModSecurity Core Rule Set (CRS), the most widely used rule set for ModSecurity. The OWASP CRS is community‑maintained and has been tuned through wide exposure to block a broad range of attacks with very few false positives.
The OWASP CRS blocks many new web application vulnerabilities out of the gate. For example, the recent Drupalgeddon 2 vulnerability (CVE-2018-7600) is correctly identified and blocked as an RCE vulnerability by NGINX ModSecurity WAF with the CRS. As of June 2018, there are more than 115,000 websites still vulnerable to Drupalgeddon 2.
For attacks that are not blocked by the CRS, ModSecurity has a flexible rules language that is based on standard Perl Compatible Regular Expressions (PCRE) syntax, the same syntax NGINX uses. ModSecurity rules can be used to virtually patch vulnerabilities, which protects applications until a proper patch can be deployed (for an example, see our blog).
How Do I Get Started?
To get started using NGINX ModSecurity WAF in GCP, please contact our sales team.
To learn more about using NGINX Plus on GCP, please see our NGINX and GCP partner page.
Learn More
- NGINX ModSecurity WAF – More technical details on the NGINX ModSecurity WAF
- ModSecurity 3.0 and NGINX: Quick Start Guide – An eBook detailing how to get up and running quickly with ModSecurity and NGINX
- ModSecurity 3.0 and NGINX: Getting Started – An on‑demand webinar showing how to get started with NGINX and ModSecurity
[NGINX ModSecurity WAF officially went End-of-Sale as of April 1, 2022 and is transitioning to End-of-Life effective March 31, 2024. For more details, see F5 NGINX ModSecurity WAF Is Transitioning to End-of-Life on our blog.]