Organizations at all different phases of the digital transformation journey are adopting DevOps practices to make app development and deployment more efficient. At the same time, one requirement remains paramount: apps must be protected from malicious traffic. In support of that goal, many organizations are applying a common DevOps practice – monitoring app performance after deployment for insights into required fixes or potential new features – to security as well. In particular, they’re using threat visibility and analytics tools that reveal what malicious traffic consists of and what part of the app it is targeting.
Threat visibility enables security (SecOps) and development (AppDev) teams to monitor security compliance and assess changes to the threat surface of apps as new app versions get released. As with monitoring the performance of new app versions for actionable insights, when security visibility is augmented with actionable analytics, SecOps can prevent potential threats, respond to actual threats in a timely way, and mitigate false positives. The result is an improved app security posture and a more secure app.
The Challenges of Threat Visibility for Modern Apps
While DevOps means organizations are changing their app development and deployment methodology, the apps they are building are changing too. Increasingly, organizations are moving to “modern apps”, which tend to be API‑centric, cloud‑enabled, and built with a microservices architecture. Such apps require an approach to threat visibility that’s different from the policies and practices for traditional monoliths. Modern apps are made up of many modular components, which greatly increases the threat surface.
The following statistics illustrate some of today’s challenges in app threat visibility:
- Businesses today face an average of 450,000 new potential threats every day.
- According to the Ponemon Cost of Malware Containment report, security teams can expect to log almost 17,000 malware alerts in a typical week.
- Hackers launch an attack every 39 seconds, an average of 2,244 times per day.
- Various studies show that security professionals are blind to more than 50% of threats targeting their apps.
- The top two operational security headaches SecOps teams are struggling with are compliance (34%) and lack of visibility into cloud security (33%).
Rapid cloud adoption (87% of enterprises are now multi‑cloud) adds an extra element of complexity, because now app threat visibility needs to be consistent across multiple application architectures and infrastructures.
Addressing these challenges to app threat visibility requires an app‑centric threat detection model built for modern app environments, one that provides a real‑time view of security events and security metrics across your apps and services regardless of the underlying infrastructure.
Threat Visibility and Analytics with NGINX Controller App Security
The NGINX Controller App Security add‑on for Controller Application Delivery provides an app‑centric self‑service model to address the security needs of modern apps. For an introduction, see Introducing the NGINX Controller App Security Add‑On for Application Delivery.
Threat Detection
Threats need to be identified before they can be presented for visibility and analytics. NGINX Controller App Security uses NGINX App Protect as the web application firewall (WAF) enforcement engine on the datapath. You define security policies (sets of security controls) in App Security and apply them to NGINX App Protect, which uses them to inspect application traffic and detect violations. NGINX App Protect uses a combination of various types of signature‑based detection (including attack signatures, threat campaign signatures, and bot signatures), anomaly‑based detection, and positive security hardening to identify threats from app traffic. Once malicious traffic is suspected or blocked, Controller App Security collects data for security events and security metrics.
Threat Visibility and Analytics
App Security enables you to assess security compliance with views of the threat origins, threat vectors, and threat targets that impact your apps. You get a detailed picture of your apps’s threat surface and specific areas of risk.
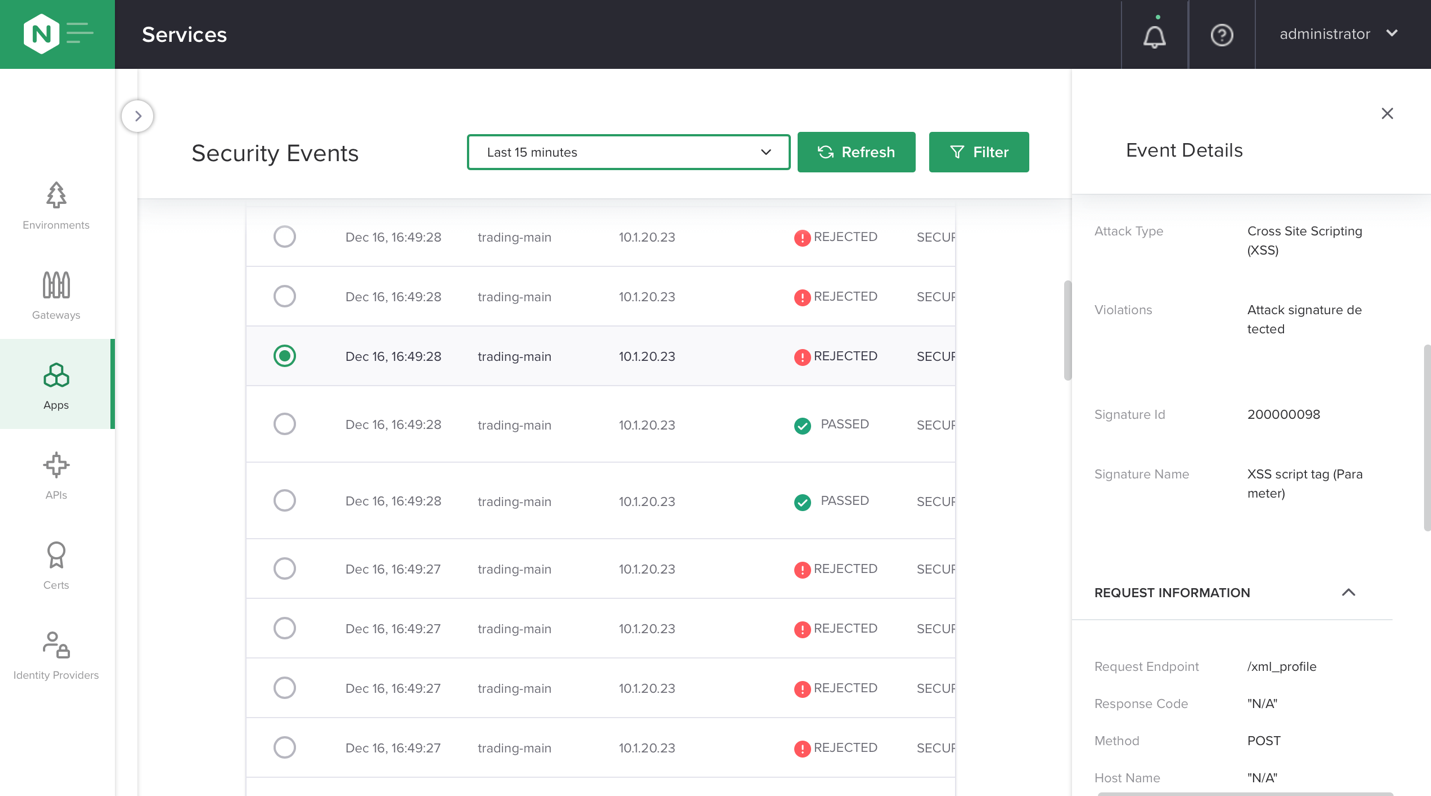
App Security generates and displays a security event whenever a request to your application is blocked as malicious traffic or flagged as potentially malicious traffic. The Security Events page provides an overview of all traffic with violations that is targeting your app, but also gives you the ability to review and filter the details of specific requests down to the attack request attribute, and attack information which includes the type of WAF attack and the violations for each request and the source IP address of the attack.
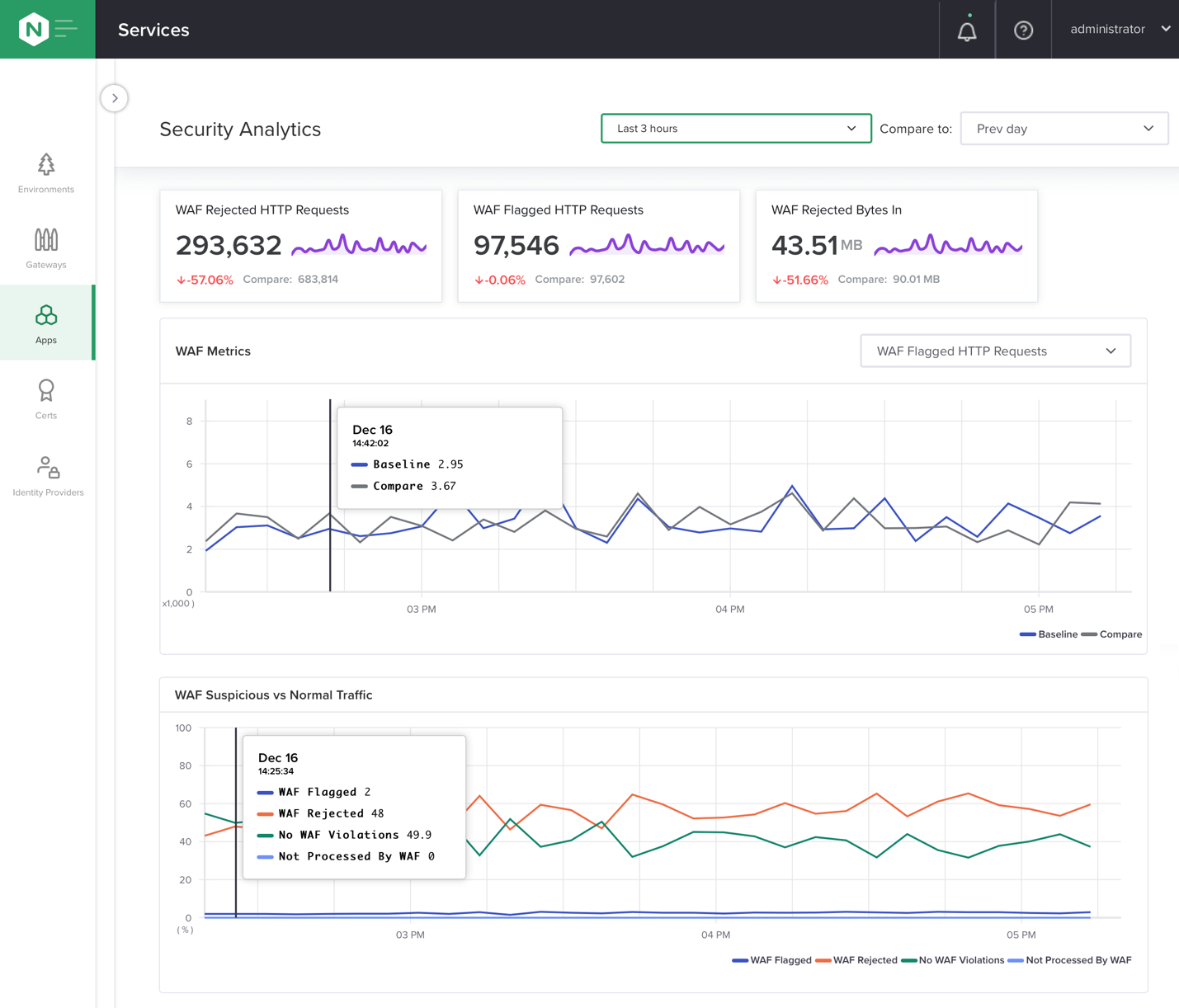
App Security collects security metrics along with security events. The Overview tab on the Security Analytics page displays violations on processed traffic such as URIs, files, and other target application resources, as well as information about threat vectors including signature counts and attack types.
The Security Analytics page also provides aggregated metrics to give you real‑time and comparative insights into your app security posture.
Once you have insight from App Security’s visibility and analytics engine, you can use App Security to tune your security policies. This is especially important for mitigating false positives. App Security understands the full context around the NGINX App Protect enforcement engine and allows you to push configurations and perform actions to harden your security policy and reduce false positives. For example, from the WAF Tuning tab on the Security Analytics page, you can identify the top individual signatures blocking your app and disable the signature for a specific app component.
Ready to try NGINX Controller App Security? Start your free 30‑day trial of NGINX Controller, NGINX Plus, and NGINX App Protect:
- At MyF5, create an account if you don’t already have one, and log in.
- On your MyF5 Dashboard page, click the Try NGINX Controller button.
For technical specifications and complete installation instructions, see the NGINX Controller documentation.